Why Network and Security Services Rhode Island Businesses Rely On Have Never Mattered More
Network and security services Rhode Island businesses depend on are no longer optional — they are a core part of staying operational, competitive, and compliant.
Here is a quick overview of what local commercial organizations need to know:
| Topic | Key Takeaway |
|---|---|
| Top threats | Ransomware, phishing, brute force attacks, RDP breaches |
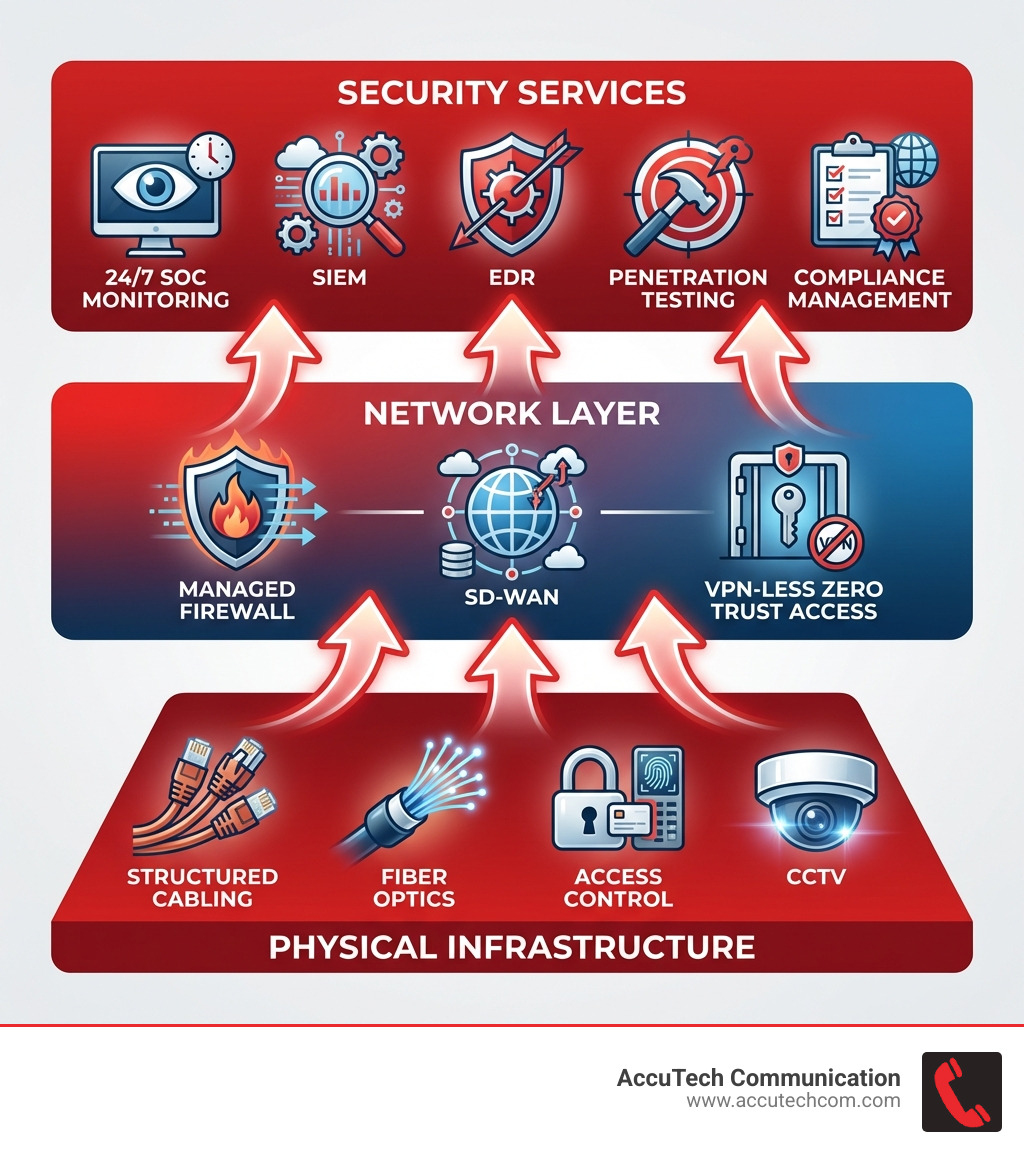
| Core services | 24/7 monitoring, SIEM, EDR, managed firewall, penetration testing |
| Key compliance standards | HIPAA, PCI-DSS, GLBA, NERC, SOC 2 |
| Critical infrastructure | Structured cabling, fiber optics, surveillance, access control |
| What to look for | US-based SOC, certified technicians (CISSP, CEH, CISA), fast response times |
Rhode Island organizations — across healthcare, manufacturing, financial services, and utilities — are facing a growing wave of cyberattacks. At the same time, aging network infrastructure is quietly creating vulnerabilities that bad actors are eager to exploit.
The reality is straightforward: a slow or poorly secured network is not just an IT problem — it is a business risk. Downtime costs money. A breach can cost far more.
Most businesses do not lack the will to fix these problems. They lack a clear picture of what a solid network and security strategy actually looks like — and who can help them build one.
This guide breaks it all down in plain language.
I’m Corin Dolan, owner of AccuTech Communications, and I’ve spent over 30 years designing and deploying commercial network infrastructure across Massachusetts, New Hampshire, and Rhode Island — including the structured cabling and physical security systems that form the foundation of any strong network and security services Rhode Island strategy. That hands-on experience is what shapes every recommendation in this guide.
Common Cyber Threats Facing Rhode Island Organizations
The digital landscape in the Ocean State is beautiful, but the threats lurking in the shadows are anything but. For Rhode Island businesses, the “it won’t happen to me” mentality is the biggest vulnerability of all. We have seen that most data breaches are actually the product of user error or poor policy rather than just a “genius hacker” movie scenario.
The “Big Five” Threats
- Ransomware: This remains the king of threats. It locks down your data and demands payment. We’ve seen local businesses hit by variants like CryptoLocker, which can halt operations instantly if you don’t have robust backups.
- Social Engineering & Phishing: This is where attackers trick your employees into giving up passwords. It’s often the “front door” for larger breaches.
- Brute Force Intrusion: Attackers use automated tools to guess passwords until they get in. If your complex password policy isn’t enforced, you’re leaving the door unlocked.
- RDP Breaches: Remote Desktop Protocol (RDP) is a common way for employees to work from home, but if it isn’t secured with a VPN or Zero Trust model, it’s a massive target.
- Keyloggers: Subtle software that records every keystroke, capturing sensitive banking info and credentials before you even know you’re infected.
As far back as the Cyber Security plan from 2015 issued by the State of Rhode Island, officials have warned that the interdependence of our networks makes every business a potential target. Whether you are a farm in Exeter tracking livestock or a law firm in Providence handling sensitive litigation, your data has a price tag on the dark web.

Essential Components of Network and Security Services Rhode Island
When we talk about Network and Security Services Rhode Island, we aren’t just talking about installing an antivirus program and calling it a day. A professional, commercial-grade defense requires several moving parts working in harmony.
The Modern Security Stack
- SIEM (Security Information and Event Management): Think of this as the “black box” of your network. It collects logs from every device and uses AI to spot patterns that indicate an attack is underway.
- EDR (Endpoint Detection and Response): This goes beyond traditional antivirus. It monitors laptops, servers, and mobile devices in real-time to block suspicious behavior.
- 24/7 SOC (Security Operations Center): Having software is great, but having a US-based SOC means real human analysts are watching your network 365 days a year. If an alarm goes off at 3:00 AM on a Sunday, they are there to stop it.
- Managed Firewall: Your first line of defense. A properly configured firewall filters incoming and outgoing traffic based on strict security rules.
However, even the best software fails if the physical “pipes” are leaky. This is where Network Cabling Services come into play. A network is only as fast and secure as its slowest component. If your business is running on outdated Category 5 cabling or messy “spaghetti” wiring in the server room, you are prone to signal loss and hardware failures that look like security breaches but are actually infrastructure collapses.
Strengthening Defenses with Network and Security Services Rhode Island
To truly secure a Rhode Island business, you have to “Know Thy Enemy.” We recommend a proactive approach that includes:
- Penetration Testing: This is “ethical hacking.” Professionals try to break into your network to show you exactly where the holes are before a criminal finds them.
- Vulnerability Assessments: Regular scans of your hardware and software to ensure everything is patched. A single unpatched piece of software is like a broken window in an otherwise locked building.
- Security Awareness Training: Since users are often the weak link, training them on acceptable use policies is vital. They should know how to spot a fake email and why they shouldn’t use the same password for their work login and their Netflix account.
When selecting a provider, look for those who hold industry-standard certifications such as:
- CISSP (Certified Information Systems Security Professional)
- CEH (Certified Ethical Hacker)
- CISA (Certified Information Systems Auditor)
- CGEIT (Certified in the Governance of Enterprise IT)
Future-Proofing with Advanced Network and Security Services Rhode Island
The way we work has changed. With more teams working remotely in places like Warwick, Cranston, and Newport, the traditional “perimeter” of the office is gone.
Modern Network and Security Services Rhode Island now lean heavily on Zero Trust Architecture. In a Zero Trust model, the network assumes no one is trustworthy by default—even if they are sitting in your office. Every user must be verified every time they access data.
We are also seeing a massive shift toward SD-WAN and Fiber Optic integration. Fiber isn’t just about speed; it’s about reliability and security. Unlike copper, fiber optics are incredibly difficult to “tap” into, making them the gold standard for secure data transmission. When we perform a Structured Cabling installation, we ensure the backbone can handle these advanced security protocols without bottlenecking.
Regulatory Compliance and Data Protection Standards
For many Rhode Island industries, security isn’t just a good idea—it’s the law. Failing to meet compliance standards can result in massive fines and loss of licensure.
- HIPAA: Essential for healthcare providers in Providence and beyond. It requires strict access controls and encryption for patient data.
- PCI-DSS: If you take credit cards, you must comply. This often involves segmenting your network so your Point of Sale (POS) system is separate from your guest Wi-Fi.
- GLBA: Critical for financial services and accounting firms.
- NERC/AWIA: Vital for utilities and water departments to protect our local infrastructure.
- SOC2: This is the “gold standard” for service organizations, ensuring data is managed securely to protect the interests of your clients.
Achieving these standards requires more than just software; it requires documented Commercial Network Cabling and physical security measures that prevent unauthorized people from walking into your server room and plugging in a thumb drive.
The Importance of Physical Infrastructure and Surveillance
It is easy to forget that “the cloud” is actually just a bunch of physical servers connected by wires. If someone can physically access your hardware, your digital security is essentially zero.
A comprehensive security plan must include:
- Structured Cabling: Organized, labeled, and tested wiring that prevents accidental outages and makes troubleshooting a breeze.
- Fiber Optics: For high-speed, secure connections between buildings or floors.
- CCTV and Surveillance: Business Security Cameras act as both a deterrent and a way to audit who has been near sensitive equipment.
- Access Control: Using keycards or biometrics to ensure only authorized personnel enter the server room or data center.
We always tell our clients: don’t let your “IT guy” give you the runaround with messy wiring. An organized telecommunications room is a secure telecommunications room. You can learn more about professional CCTV Security Camera systems to see how physical and digital security overlap.
Evaluating Costs and Choosing a Local Provider
When Rhode Island businesses look for Network and Security Services Rhode Island, cost is always a factor. However, it’s important to understand the difference between a “break/fix” model and a “proactive” model.
In a break/fix model, you only pay when something is broken. This sounds cheaper, but it’s actually much more expensive in the long run due to unpredictable downtime and emergency repair fees. A proactive, managed model provides predictable monthly costs and prevents problems before they start.
Understanding the Investment
While we cannot provide exact quotes without seeing your site, industry data for the New England region shows a wide range of costs based on the complexity of the network. For example, a basic managed security setup for a small office might range from $1,500 to over $5,000 per month depending on the number of endpoints and the level of monitoring (8×5 vs. 24×7). For larger enterprises or those requiring strict compliance, costs can easily scale to $15,000+ per month. These are average costs sourced from publicly available internet data and do not reflect the actual rates of AccuTech Communications.
| Feature | Reactive Support (Break/Fix) | Proactive Monitoring (Managed) |
|---|---|---|
| Downtime | High (Wait for something to break) | Low (Issues fixed before failure) |
| Costs | Unpredictable & Spiky | Consistent Monthly Budget |
| Security | Basic/Outdated | Continuous Updates & Patches |
| Response Time | Hours or Days | Guaranteed (often < 15 mins) |
| Strategy | None | vCIO & Long-term Planning |
When searching for a Network Cable Installer Near Me, ensure they understand both the physical and logical side of security. You want a partner who won’t just pull wire, but who understands how that wire supports your firewall, your cameras, and your compliance goals.
Frequently Asked Questions about Rhode Island IT Security
What certifications should a security provider hold?
You should look for a provider whose team holds recognized certifications such as CISSP, CEH (Certified Ethical Hacker), and CISA. These indicate a high level of expertise in identifying vulnerabilities and managing risk. Additionally, look for BICSI certifications (like RCDD) for the technicians handling your physical cabling infrastructure.
How does 24/7 monitoring prevent business downtime?
Most cyberattacks and hardware failures don’t happen during business hours. 24/7 monitoring uses automated tools and human analysts to spot “smoke” before there is a “fire.” For example, if a server fan starts to fail at 2 AM, a proactive provider can dispatch a technician to replace it before the office opens at 8 AM, preventing a total system crash.
Why is structured cabling important for network security?
Messy cabling is a security risk. It makes it difficult to identify unauthorized devices plugged into your network and increases the chance of accidental disconnections. Structured Cabling ensures that every connection is documented and tested, which is a requirement for many security audits and compliance frameworks like SOC 2.
Conclusion
Securing your business in the modern age requires a partner who understands that technology and security must always align. At AccuTech Communications, we have been helping businesses across Massachusetts, New Hampshire, and Rhode Island find that alignment since 1993.
Whether you need to overhaul your server room, install high-definition surveillance, or build a fiber optic backbone for your Providence headquarters, we provide the certified, reliable service your organization deserves. We pride ourselves on competitive pricing and a commitment to quality that has kept us in business for over three decades.
Don’t wait for a breach to realize your network is vulnerable. Schedule a Network Cabling Installation or a site audit with us today, and let’s build a foundation that keeps your business safe, fast, and future-proof.